The end is nigh for Exchange 2007: support nearing end and some other reasons to upgrade
 Reading Time: 2 minutes
Reading Time: 2 minutesThe Exchange Team blog reminded us today that in about a year the extended support for Exchange Server 2007 will end. This means no more updates of any kind, not even security updates. Feature updates already stopped 4 years earlier when Mainstream support ended. The product will continue to run, but how longer it’s being kept in production that will add some risk to your environment due to security issues not being fixed. You can find lifecycles of other Microsoft products here.
Another risk is that newer products won’t work (as intended) with Exchange 2007 anymore. For instance, Outlook 2016 won’t connect to Exchange 2007. Furthermore, features such as the Database Availability Groups far outperform (IMHO) any clustering solution available in 2007. There wasn’t any multi-browser support for OWA. And the list goes on. It’s really, really time to upgrade. Do note that you can migrate to Exchange 2013, but not to Exchange 2016 (without phasing out your last 2007 server).
Another potentially important tidbit is that Exchange 2007 SMTP, IMAP and POP3 do not support TLS1.1 and TLS1.2, it does however support TLS1.0. HTTPS is not affected by this. This (for some potentially unexpected fact) has been fixed in Exchange 2010 SP3 RU9 and 2013 CU8 just recently, but due to the support nature of Exchange 2007 it is reasonable to assume that it will not be addressed. For those who require TLS1.1/1.2 for SMTP, they will either implement another SMTP solution in front of Exchange or upgrade. For IMAP/POP3 a reverse proxy or similar solution could provide the required level of encryption.
To be clear: HTTPS services on Exchange 2007 do support TLS1.1 and TLS1.2 (when enabled). Just SMTP, IMAP and POP3 do not.
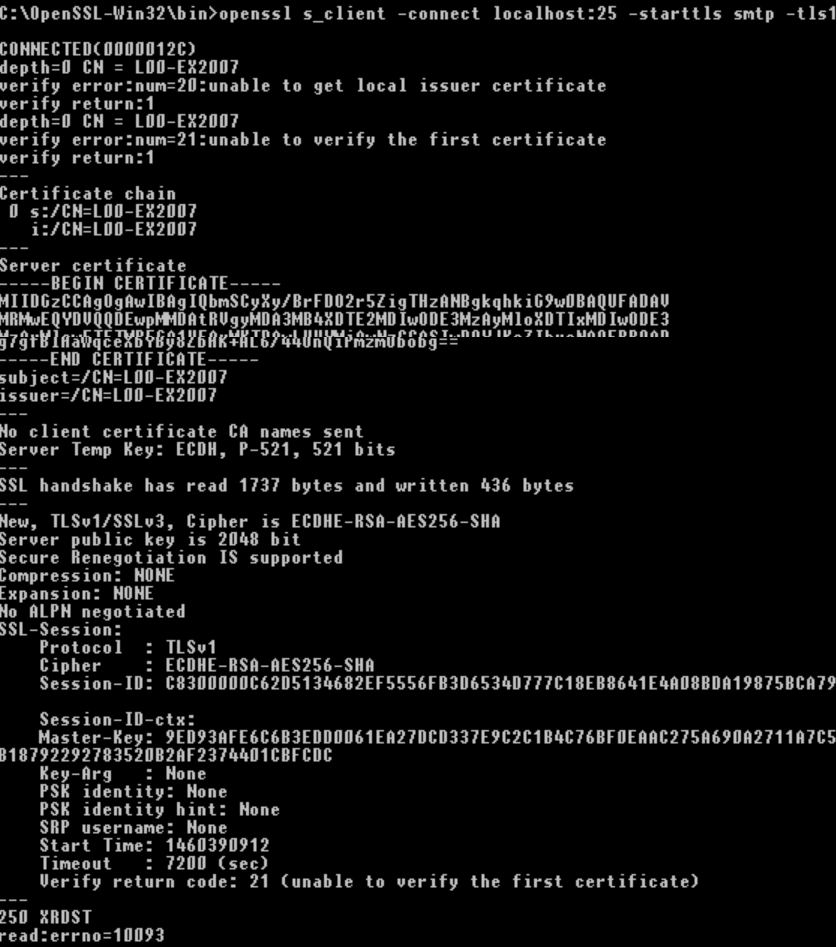
Do you want to check whether your servers supports which encryption protocol and ciphers, check my previous blog: Checking security protocols and ciphers on your Exchange servers. If you want to check supported protocols of your SMTP solution (which wasn't added in my original post), use OpenSSL for Win32 (sslscan isn't being maintained and has some downsides). The syntax would like this:
openssl s_client -connect <fqdn>:25 -starttls smtp
Add -ssl3, -tls1, -tls1_1, -tls1_2 to test specific protocols. If you don’t get a Server Certificate, the protocol is probably not supported.